IT Consulting | IT Support | Managed Services | New Jersey Computer Support Services
Every week we are introduced to new threats, we cannot stress enough how important user awareness is in defense against these types of attacks. As soon as these threats are uncovered, another has already been created. These crimes advance with technology, and as we all know technology is advancing faster than ever. In phishing scams like this week’s, the attacker takes advantage of the most vulnerable aspect of any business computer network, the employees.
We cannot stress enough that in order for your network to be secure, all employees must be properly
trained on safe internet and email use. The most important thing we suggest is to not respond to the
suspicious email or open any links. If you are questioning the email, we suggest calling any phone
number on the document to verify its authenticity. Even then, you must keep your guards up and not
divulge any personal information until the validity of the sender is confirmed.
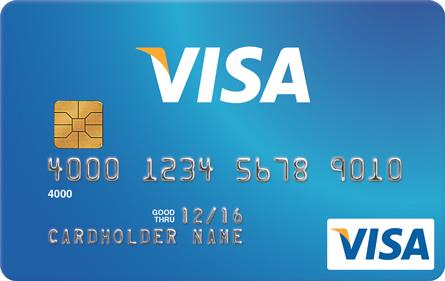
Recently credit cards have been updating their technology. Many companies are redesigning their
cards to incorporate a security chip. Old credit cards traditionally transfer data with the magnetic
strip on the back, recently this technology is being replaced with new EMV chip technology. This new
chip adds a new layer of security to the credit card focusing on fraud detection.
This new chip is a great technology advance in security, but with the advance opens the door for
phishing scams. The victim will receive an email that looks completely legitimate, containing up to
date logs and all! The email will then ask the victim to verify a few pieces personal information
and they will send the new updated card right away. Now the attacker has all the victims’
personal information along with their credit card number. You must keep in mind that your bank will
never ask you to disclose personal information via email.
This is your classic phishing scam in order to steal someone’s identity. This can happen to
one person, or the entire billing department of a company. This is why we constantly stress the
importance of end user security awareness. Before you become the next victim, consult with ICS on
ways to enhance end user awareness.
About Us:
- 200+ 5-Star Google Rated IT Firm
- Microsoft Certified Cloud AI Partner
- SOC II Certified Managed Service Provider
- Better Business Bureau A+ Rated






